key card copy - Fast & Reliable Top1-5
# Key Card Copy: Understanding the Technology and Its Implications
## Introduction to Key Card Copy Technology
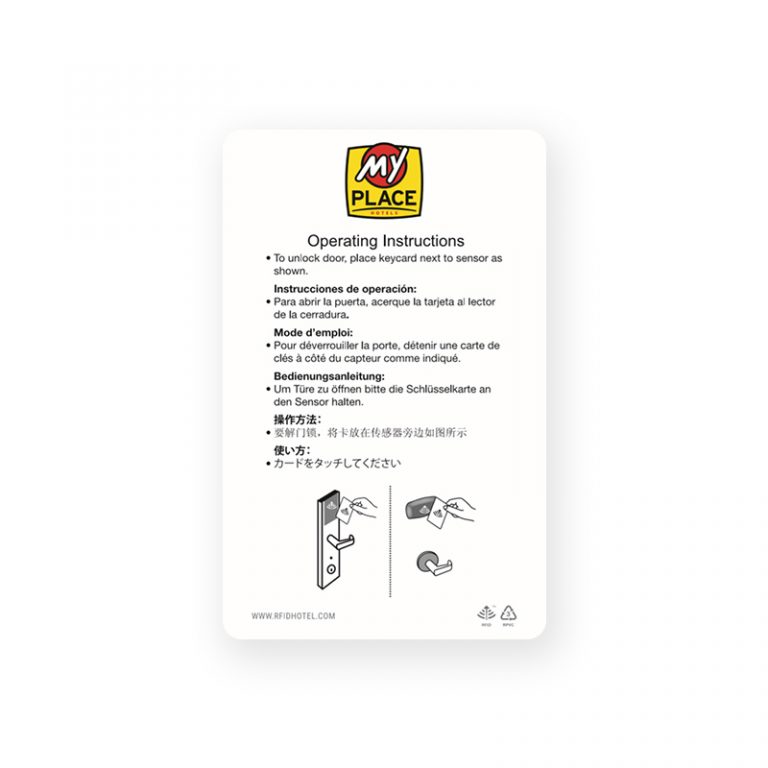
Key card copy refers to the process of duplicating or cloning access cards that use RFID (Radio-Frequency Identification) or NFC (Near Field Communication) technology. These cards are widely used in hotels, offices, residential buildings, and various secure facilities for access control. The ability to copy key cards has raised significant concerns regarding security, privacy, and the integrity of access control systems.
 ## How Key Card Copy Works
## How Key Card Copy Works
 ### RFID and NFC Technology Basics
### RFID and NFC Technology Basics

 RFID and NFC are wireless communication technologies that allow data transfer between devices over short distances. RFID operates at various frequencies (LF, HF, UHF) and is commonly used for access control, inventory management, and identification. NFC is a subset of RFID that operates at 13.56 MHz and is designed for close-range communication, typically within 4 centimeters.
RFID and NFC are wireless communication technologies that allow data transfer between devices over short distances. RFID operates at various frequencies (LF, HF, UHF) and is commonly used for access control, inventory management, and identification. NFC is a subset of RFID that operates at 13.56 MHz and is designed for close-range communication, typically within 4 centimeters.
 **Key Card Copy** involves reading the data stored on an original card and writing it to a blank card or device. This process can be achieved using specialized hardware and software designed to interact with RFID/NFC chips.
### Common Types of Key Cards
1. **MIFARE Classic**: One of the most common RFID cards, using proprietary encryption. However, vulnerabilities have been discovered, making them susceptible to cloning.
2. **MIFARE DESFire**: More secure than MIFARE Classic, using AES encryption.
3. **HID Prox**: Low-frequency cards often used in older access systems.
4. **iClass**: Higher security cards with encryption capabilities.
5. **NFC Cards**: Used in smartphones and modern access systems, supporting various protocols like ISO 14443.
## Personal Experience with Key Card Systems
During my time working as a security consultant, I encountered numerous cases where organizations faced security breaches due to key card cloning. One particular incident involved a corporate office where an employee cloned t
**Key Card Copy** involves reading the data stored on an original card and writing it to a blank card or device. This process can be achieved using specialized hardware and software designed to interact with RFID/NFC chips.
### Common Types of Key Cards
1. **MIFARE Classic**: One of the most common RFID cards, using proprietary encryption. However, vulnerabilities have been discovered, making them susceptible to cloning.
2. **MIFARE DESFire**: More secure than MIFARE Classic, using AES encryption.
3. **HID Prox**: Low-frequency cards often used in older access systems.
4. **iClass**: Higher security cards with encryption capabilities.
5. **NFC Cards**: Used in smartphones and modern access systems, supporting various protocols like ISO 14443.
## Personal Experience with Key Card Systems
During my time working as a security consultant, I encountered numerous cases where organizations faced security breaches due to key card cloning. One particular incident involved a corporate office where an employee cloned t
 ## How Key Card Copy Works
## How Key Card Copy Works
 ### RFID and NFC Technology Basics
### RFID and NFC Technology Basics

 RFID and NFC are wireless communication technologies that allow data transfer between devices over short distances. RFID operates at various frequencies (LF, HF, UHF) and is commonly used for access control, inventory management, and identification. NFC is a subset of RFID that operates at 13.56 MHz and is designed for close-range communication, typically within 4 centimeters.
RFID and NFC are wireless communication technologies that allow data transfer between devices over short distances. RFID operates at various frequencies (LF, HF, UHF) and is commonly used for access control, inventory management, and identification. NFC is a subset of RFID that operates at 13.56 MHz and is designed for close-range communication, typically within 4 centimeters.
 **Key Card Copy** involves reading the data stored on an original card and writing it to a blank card or device. This process can be achieved using specialized hardware and software designed to interact with RFID/NFC chips.
### Common Types of Key Cards
1. **MIFARE Classic**: One of the most common RFID cards, using proprietary encryption. However, vulnerabilities have been discovered, making them susceptible to cloning.
2. **MIFARE DESFire**: More secure than MIFARE Classic, using AES encryption.
3. **HID Prox**: Low-frequency cards often used in older access systems.
4. **iClass**: Higher security cards with encryption capabilities.
5. **NFC Cards**: Used in smartphones and modern access systems, supporting various protocols like ISO 14443.
## Personal Experience with Key Card Systems
During my time working as a security consultant, I encountered numerous cases where organizations faced security breaches due to key card cloning. One particular incident involved a corporate office where an employee cloned t
**Key Card Copy** involves reading the data stored on an original card and writing it to a blank card or device. This process can be achieved using specialized hardware and software designed to interact with RFID/NFC chips.
### Common Types of Key Cards
1. **MIFARE Classic**: One of the most common RFID cards, using proprietary encryption. However, vulnerabilities have been discovered, making them susceptible to cloning.
2. **MIFARE DESFire**: More secure than MIFARE Classic, using AES encryption.
3. **HID Prox**: Low-frequency cards often used in older access systems.
4. **iClass**: Higher security cards with encryption capabilities.
5. **NFC Cards**: Used in smartphones and modern access systems, supporting various protocols like ISO 14443.
## Personal Experience with Key Card Systems
During my time working as a security consultant, I encountered numerous cases where organizations faced security breaches due to key card cloning. One particular incident involved a corporate office where an employee cloned t