clone nfc card - Fast & Reliable Top1-5
# Clone NFC Card: A Comprehensive Guide to Understanding and Safeguarding Your Digital Identity
## Introduction to NFC Card Cloning
In today's digital age, the ability to **clone NFC card** technology has become both a fascinating technical capability and a significant security concern. Near Field Communication (NFC) cards have revolutionized how we interact with secure systems, from building access controls to payment methods and public transportation. The process to **clone NFC card** devices involves replicating the data stored on an original card onto another compatible device, creating a functional duplicate that can interact with the same systems as the original.
### How NFC Technology Works
NFC operates on the principle of electromagnetic induction, allowing two devices to communicate when brought within close proximity (typically 4 centimeters or less). This technology enables contactless data exchange between devices like smartphones, tablets, and specially designed cards. When you **clone NFC card** technology, you're essentially copying the unique identifier and data stored in the card's chip to create a working replica.
## Technical Specifications of Common NFC Cards
 When considering how to **clone NFC card** technology, it's essential to understand the technical parameters of common NFC implementations:
**MIFARE Classic 1K Specifications:**
- Memory: 1KB EEPROM
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
When considering how to **clone NFC card** technology, it's essential to understand the technical parameters of common NFC implementations:
**MIFARE Classic 1K Specifications:**
- Memory: 1KB EEPROM
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
 - Chip Code: NXP MF1S50YYX_V1
- Dimensions: Standard ISO/IEC 7810 ID-1 format (85.60 × 53.98 × 0.76 mm)
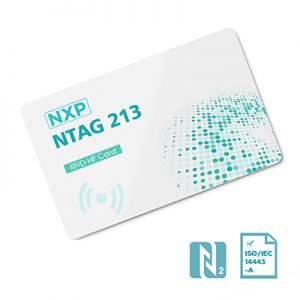
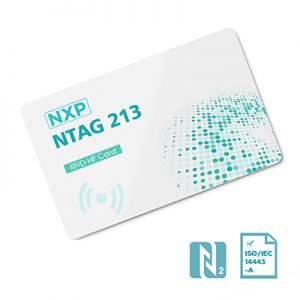
**NTAG213 Specifications:**
- Memory: 144 bytes user memory
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
- Chip Code: NXP NTAG213
- Dimensions: Various form factors available
- Chip Code: NXP MF1S50YYX_V1
- Dimensions: Standard ISO/IEC 7810 ID-1 format (85.60 × 53.98 × 0.76 mm)
**NTAG213 Specifications:**
- Memory: 144 bytes user memory
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
- Chip Code: NXP NTAG213
- Dimensions: Various form factors available
 **MIFARE DESFire EV2 Specifications:**
- Memory: 2KB/4KB/8KB options
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: Up to 848 kbit/s
**MIFARE DESFire EV2 Specifications:**
- Memory: 2KB/4KB/8KB options
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: Up to 848 kbit/s
 - Chip Code: NXP MF3D(H)x2
- Security: AES-128 encryption
- Chip Code: NXP MF3D(H)x2
- Security: AES-128 encryption
 *Note: These technical parameters are reference data only. For specific applications, please contact backend management.*
## Legitimate Applications of NFC Cloning
### Personal Convenience and Backup Solutions
From my personal experience working with digital security systems, I've found that learning how to **clone NFC card** technology for legitimate purposes can significantly enhance daily convenience. Many people use this capability to create backup copies of their access cards in case of loss or damage. I remember helping a colleague who had lost their office access card just before an important me
*Note: These technical parameters are reference data only. For specific applications, please contact backend management.*
## Legitimate Applications of NFC Cloning
### Personal Convenience and Backup Solutions
From my personal experience working with digital security systems, I've found that learning how to **clone NFC card** technology for legitimate purposes can significantly enhance daily convenience. Many people use this capability to create backup copies of their access cards in case of loss or damage. I remember helping a colleague who had lost their office access card just before an important me
 When considering how to **clone NFC card** technology, it's essential to understand the technical parameters of common NFC implementations:
**MIFARE Classic 1K Specifications:**
- Memory: 1KB EEPROM
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
When considering how to **clone NFC card** technology, it's essential to understand the technical parameters of common NFC implementations:
**MIFARE Classic 1K Specifications:**
- Memory: 1KB EEPROM
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
 - Chip Code: NXP MF1S50YYX_V1
- Dimensions: Standard ISO/IEC 7810 ID-1 format (85.60 × 53.98 × 0.76 mm)
**NTAG213 Specifications:**
- Memory: 144 bytes user memory
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
- Chip Code: NXP NTAG213
- Dimensions: Various form factors available
- Chip Code: NXP MF1S50YYX_V1
- Dimensions: Standard ISO/IEC 7810 ID-1 format (85.60 × 53.98 × 0.76 mm)
**NTAG213 Specifications:**
- Memory: 144 bytes user memory
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: 106 kbit/s
- Chip Code: NXP NTAG213
- Dimensions: Various form factors available
 **MIFARE DESFire EV2 Specifications:**
- Memory: 2KB/4KB/8KB options
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: Up to 848 kbit/s
**MIFARE DESFire EV2 Specifications:**
- Memory: 2KB/4KB/8KB options
- Operating Frequency: 13.56 MHz
- Data Transfer Rate: Up to 848 kbit/s
 - Chip Code: NXP MF3D(H)x2
- Security: AES-128 encryption
- Chip Code: NXP MF3D(H)x2
- Security: AES-128 encryption
 *Note: These technical parameters are reference data only. For specific applications, please contact backend management.*
## Legitimate Applications of NFC Cloning
### Personal Convenience and Backup Solutions
From my personal experience working with digital security systems, I've found that learning how to **clone NFC card** technology for legitimate purposes can significantly enhance daily convenience. Many people use this capability to create backup copies of their access cards in case of loss or damage. I remember helping a colleague who had lost their office access card just before an important me
*Note: These technical parameters are reference data only. For specific applications, please contact backend management.*
## Legitimate Applications of NFC Cloning
### Personal Convenience and Backup Solutions
From my personal experience working with digital security systems, I've found that learning how to **clone NFC card** technology for legitimate purposes can significantly enhance daily convenience. Many people use this capability to create backup copies of their access cards in case of loss or damage. I remember helping a colleague who had lost their office access card just before an important me